by ChatGPT
Introduction
When building an API or any system that handles large volumes of requests, one crucial challenge you’ll face is how to manage and control traffic. Enter rate limiting — the process that ensures your system doesn’t get overwhelmed by too many requests at once. Whether it’s to prevent abuse, ensure fairness, or just to keep things running smoothly, understanding the right way to implement rate limiting is essential. This article will walk you through the different types of rate limiters, their real-world applications, and how to design an effective one for your system.
How Rate Limiting Works and Why Use It
How Rate Limiting Works
Rate limiting typically involves tracking the number of requests a user or client makes within a specified time frame (like seconds, minutes, or hours). If the user exceeds the allowed number of requests, the system blocks or delays the excess requests until the next time window begins.
Here’s a simple flow of how it works:
- Request is made: A user sends a request to the system.
- Check request count: The system checks how many requests the user has made in the current time window.
- Check against limit: If the user has made too many requests, the system responds with an error (commonly HTTP 429 — Too Many Requests). If the limit hasn’t been reached, the request is processed as usual.
- Window resets: Once the time window expires, the request count is reset, and the user can make new requests within the limit.
Press enter or click to view image in full size
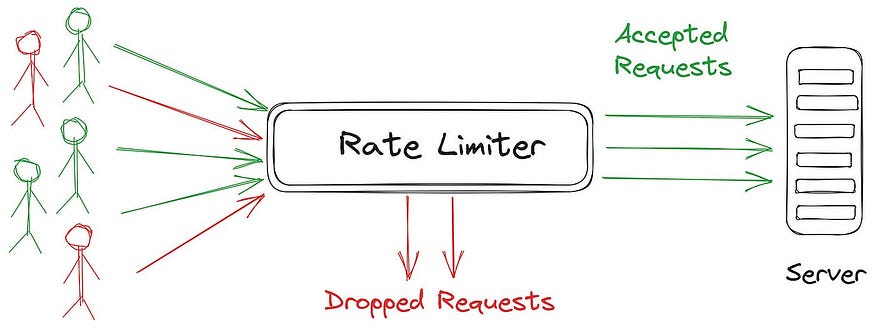
How rate limiting works
Depending on the algorithm used, the method for counting and handling requests varies, but the basic principle remains the same.
Why Use Rate Limiting?
- Prevent Overload:
Too many requests at once can overwhelm your servers, leading to crashes or degraded performance. By controlling the flow of traffic, rate limiting ensures that your system can handle the load without going down. - Fairness:
Without rate limiting, some users could hog resources, leaving others with a poor experience. By limiting the number of requests, you ensure that all users get a fair share of the system’s capacity. - Protect from Abuse:
Rate limiting helps prevent malicious users from exploiting your system. For example, a malicious actor could try to flood your API with requests to crash it or scrape sensitive data. Rate limiting ensures they can’t make too many requests in a short time.
Key Rate Limiting Algorithms
When choosing a rate limiter, the algorithm you pick depends on your use case. Each approach comes with its own advantages and trade-offs. Let’s take a look at the most common algorithms used in rate limiting, and when you might want to use them.
1. Token Bucket
The Token Bucket algorithm is one of the most flexible and widely used for rate limiting. It’s designed to allow for bursts of traffic while maintaining a steady flow of requests. Here’s how it works:
Parameters:
- Bucket capacity: Maximum number of tokens the bucket can hold.
- Token refill rate: Rate at which tokens are added to the bucket (e.g., 1 token per second).
- Request rate: Number of tokens required per request.
How it works: Tokens are generated at a fixed rate and placed into a bucket. Each incoming request consumes a token. If there are tokens available, the request proceeds. If the bucket is empty, requests are delayed or blocked. The refill rate ensures that the system can handle bursts of traffic by temporarily allowing extra requests.
Press enter or click to view image in full size
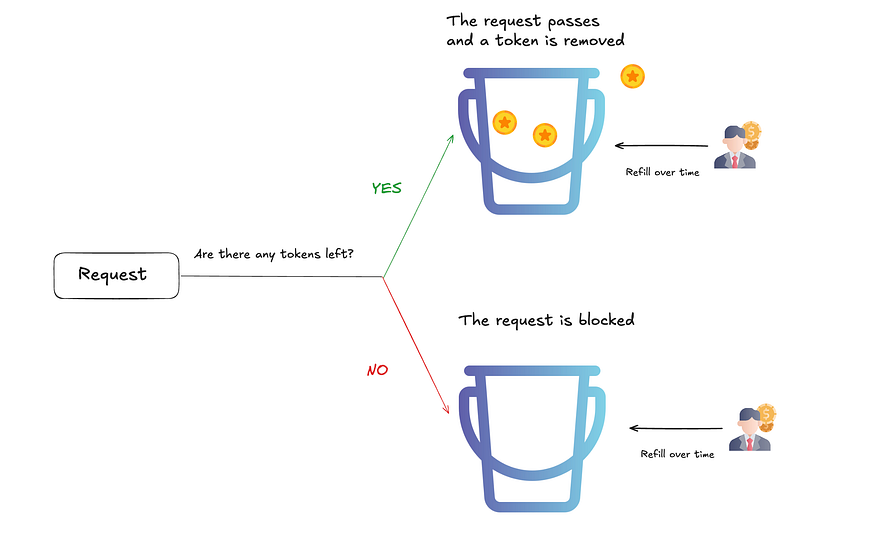
Token bucket visualized
Why use it? The token bucket is perfect for situations where you need to handle bursts of traffic, like when users submit multiple requests within a short period. It allows for burst behavior but limits the overall rate over time.
Real-World Use Case:
Imagine an online ticketing platform during a flash sale. Users might attempt to book tickets in bulk within a few seconds, creating a surge in requests. The token bucket ensures that the platform can handle the initial burst of requests but throttles back once the tokens are exhausted, preventing overload.
2. Leaky Bucket
The Leaky Bucket algorithm is similar to the token bucket but with a key difference in how traffic is handled. While the token bucket allows bursts and smooths out traffic over time, the leaky bucket enforces a more rigid output rate.
Get Tariq Massaoudi’s stories in your inbox
Join Medium for free to get updates from this writer.
Subscribe
Parameters:
- Bucket capacity: Maximum number of requests the bucket can hold.
- Leak rate: Fixed rate at which requests are processed (e.g., 10 requests per second).
- Request arrival rate: Rate at which requests arrive at the system.
How it works: Requests are added to the bucket. If the bucket overflows (i.e., too many requests arrive), the excess requests are dropped. The leak rate controls how quickly requests are processed and ensures a smooth flow over time.
Press enter or click to view image in full size
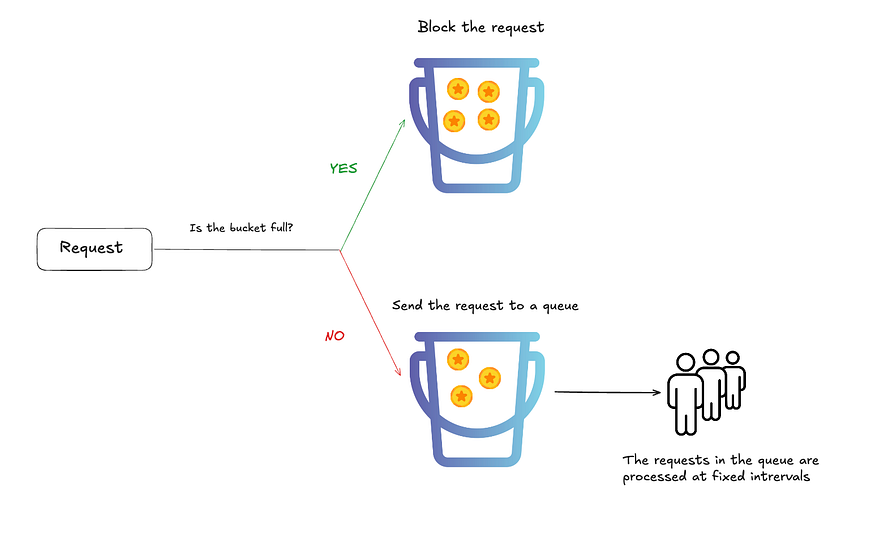
Leaky bucker visualized
Why use it? The leaky bucket is great when you want to maintain a steady, consistent rate of requests. It’s less flexible than the token bucket but can be ideal for systems that need to avoid sudden spikes in traffic.
Real-World Use Case:
Consider a live-streaming service where users upload video content. You don’t want the server to be overwhelmed with too many concurrent uploads, so you regulate the rate at which uploads are processed. This ensures that while multiple users can upload content, the server doesn’t get bogged down by too many uploads at once.
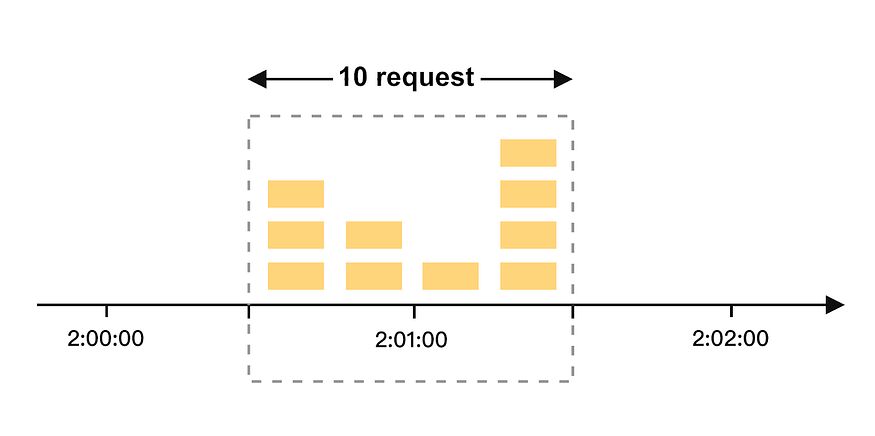
3. Fixed Window Counter
The Fixed Window Counter algorithm is the simplest form of rate limiting. It tracks the number of requests within a fixed time window, and if the number of requests exceeds the threshold, further requests are blocked until the next window starts.
Parameters:
- Time window**:** The time frame in which requests are counted (e.g., 1 minute).
- Max requests per window: The maximum number of requests allowed within the time window.
How it works: The system tracks the number of requests made within a fixed time window (e.g., 1 minute). If the number of requests exceeds the limit during that window, the system blocks further requests until the next time window begins.
Press enter or click to view image in full size

Fixed window counter visualized
Why use it? This algorithm is ideal for applications where traffic is consistent and predictable. It’s simple and effective.
Cons:
- One major downside of using the Fixed Window Counter is the spike in traffic at the edges of the window. For example, if a user makes 99 requests just before the end of the time window and then another 99 immediately after the window resets, it could result in 198 requests being processed within a very short time, much more than the allowed quota. This can cause unexpected load on the system.
Real-World Use Case:
Think of a public API for checking stock prices. Each user is allowed 100 requests per minute. If a user exceeds this limit, they can’t make further requests until the next minute. The fixed window is perfect for this case, where users are making regular requests at a steady rate.
4. Sliding Window Log
The Sliding Window Log algorithm provides more precision by tracking individual request timestamps within a sliding window. It ensures that requests are spread evenly across the time period, avoiding the burst behavior of the fixed window counter.
Parameters:
- Time window: The length of the sliding window (e.g., 1 minute).
- Max requests: The maximum number of requests allowed within the window.
- Request timestamps: Track the exact time each request was made.
How it works: Requests are timestamped as they come in. The system tracks how many requests are made within the sliding window (e.g., the last 1 minute). The excess requests are blocked or delayed if the number of requests exceeds the allowed limit within the window.
Press enter or click to view image in full size
Sliding window counter visualized
- Why use it? This algorithm is ideal when you need more granular control over request distribution across time. It ensures that requests are evenly distributed within the window, avoiding bursts at the beginning or end.
Real-World Use Case:
A mobile banking app allows users to make 10 transactions per day. With the sliding window log, the system ensures that the user doesn’t exceed the transaction limit, regardless of when the transactions are spread out across the day.
Rate limiters in the cloud
If you’re working with cloud platforms, there’s no need to reinvent the wheel. Both AWS and Azure offer built-in rate limiting features that are easy to integrate and scale.
- AWS API Gateway: AWS offers built-in rate limiting for APIs. You can set limits on the number of requests per second, minute, or hour per user or API key. It also integrates with AWS Lambda for more advanced traffic management.
- Azure API Management: Azure provides API Management, which allows you to enforce rate limits and quotas at the API level. You can define policies to throttle requests based on user or IP address, and scale these limits as needed.
Conclusion
To wrap things up, rate limiting is crucial for maintaining a smooth, fair, and secure system. Whether you’re dealing with burst traffic or protecting your backend from abuse, rate limiting helps you keep things under control. Of course, there are trade-offs; some algorithms are simpler but less flexible, while others offer more precision but come with added complexity. We’ve covered key algorithms like Token Bucket, Leaky Bucket, Fixed Window Counter, and Sliding Window Log, and seen how they fit different use cases. If you’re in the cloud, AWS API Gateway and Azure API Management offer powerful, managed solutions that take care of the heavy lifting. So, choose the right algorithm or service for your needs, and you’ll have a system that handles traffic efficiently and scales with ease. Thanks for reading, and I hope this article has given you the insights you need to tackle rate limiting in your projects.